 If you are coming to the OpenStack summit in San Diego next week then please find me at the show! I want to hear from you about the Foundation, community, OpenStack deployments, Crowbar and anything else. Oh, and I just ordered a handful of Crowbar stickers if you wanted some CB bling.
If you are coming to the OpenStack summit in San Diego next week then please find me at the show! I want to hear from you about the Foundation, community, OpenStack deployments, Crowbar and anything else. Oh, and I just ordered a handful of Crowbar stickers if you wanted some CB bling.
Matt Ray (Opscode), Jason Cannavale (Rackspace) and I were Ops track co-chairs. If you have suggestions, we want to hear. We managed to get great speakers and also some interesting sessions like DevOps panel and up streaming deploy working sessions. It’s only on Monday and Tuesday, so don’t snooze or you’ll miss it.
My team from Dell has a lot going on, so there are lots of chances to connect with us:
- Monday
- Crowbar session (including Crowbar2) by Scott Jensen @ 9:50
- Pull From Source (DevOps on steroids!) by Andi Abes @ 11:50
- Folsom to Grizzly migration ops strategy by Greg Althaus @ 4:30
- Swift Automatic Ring construction by Andi Abes
- Tuesday
- Quantum Fog (Cloud API abstraction networking) by me @ 11:50
- Distribution Panel sponsored by Dell with SUSE, Canonical, Redhat and others @ 3:40
- Wednesday
- Crowbar 2 mini summit (TBD)
- Community Meetups with Kamesh Pemmaraju and Sean Roberts @ 2:40
- Friday – I’ll be at the beach cleanup.
At the Dell booth, Randy Perryman will be sharing field experience about hardware choices. We’ve got a lot of OpenStack battle experience and we want to compare notes with you.
I’m on the board meeting on Monday so likely occupied until the Mirantis party.
See you in San Diego!
PS: My team is hiring for Dev, QA and Marketing. Let me know if you want details.
 I could not be happier with the results Crowbar collaborators and
I could not be happier with the results Crowbar collaborators and 

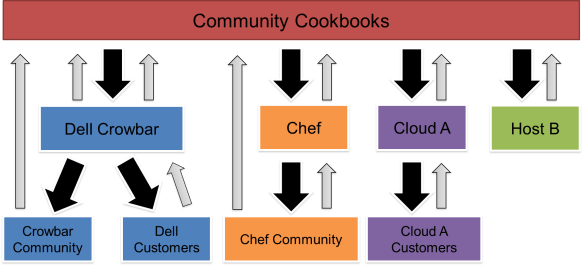
 I also see that community driven work is positioning Crowbar to break beyond being platforms for OpenStack and Apache Hadoop solutions that pay the bills for
I also see that community driven work is positioning Crowbar to break beyond being platforms for OpenStack and Apache Hadoop solutions that pay the bills for  When Greg Althaus and I first proposed the project that would become
When Greg Althaus and I first proposed the project that would become 
 Nearly a year ago at
Nearly a year ago at 

 Curious about
Curious about